Personally Verify Your Vote Is Accurately Submitted & Counted In The Final Tally
Verification Number
When you submit your vote, your device generates a unique, randomly generated secret Verification Number. This number acts as a personal tool that allows you to confirm, with complete certainty, that your vote was properly recorded and counted.
This method provides a higher level of assurance than paper elections, where you have limited opportunities for first-hand verification after casting your ballot. This is sometimes referred to as “End-to-End Voter Verifiability”.
After casting your ballot, your device continues to store your personal Verification # in the browser memory:
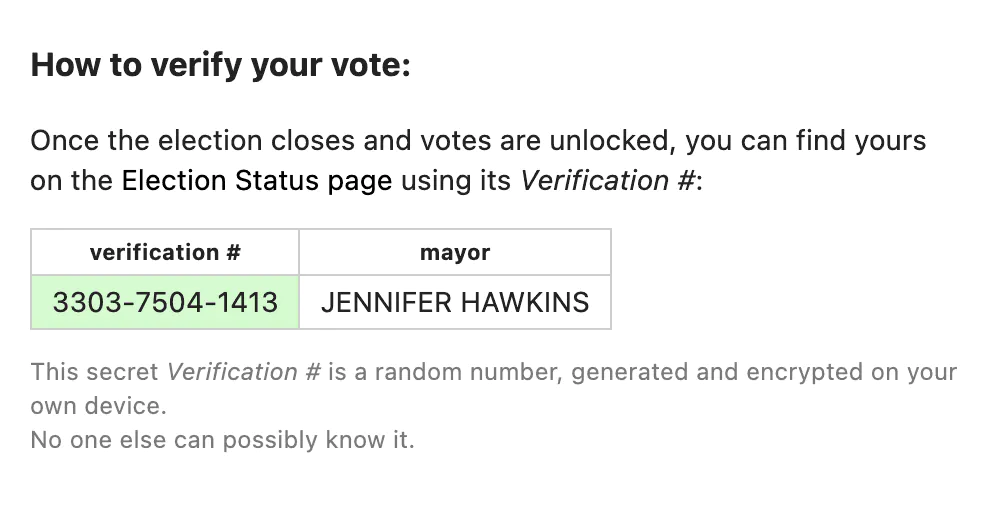
At the end of the election when the list of votes is published, you can use your Verification # to verify if your vote is in the list and if it accurately reflects your choices:

If a vote cannot be confirmed, the standard SIV protocol for Remediating Compromised Votes can be used, so that the voter can submit their replacement selections.
Quicker Multi-Device Checks for Malware
In order to provide another layer of security against malware threats, SIV also provides a process you can quickly use on a second device to confirm your selections, which can be initiated right at the time of vote, without waiting for election results to be unlocked.
See: Using Multiple Devices to Detect Malware.
Manual Verification
It is also possible to verify election results without requiring any correct digital computation.
Instead, manual verification works by double checking with other people’s devices or paper printouts.
Verifying the accuracy of your vote selections on other people’s devices provides additional resistance because every device would need to be compromised by coordinating malware. Additionally, if you check manually, the second device would need to know specifically which vote is yours, making it even harder to hide cheating.
Paper printouts of anonymized election votes can be made accessible in public locations such as Departments of Elections, local libraries, or brought to voters by auditors. This allows voters to check in-person with their Verification # if their vote selections are accurately recorded.
Although using other people’s devices or paper printouts may seem time-consuming, with statistical sampling, only a surprisingly small number of people verifying this analog way can be used to calibrate the more accessible digital verification methods, to achieve very high confidence in the outcome.